authentication type smart card type 1 type 2 Something you know – Type 1 Authentication (passwords, pass phrase, PIN . An NFC USB Reader/Writer that works for your Windows or Mac desktop computer. Download a free desktop app to use this NFC writer. Great for reading or writing NFC tags in bulk quickly and efficiently. Similar to smartphones, tap NFC chip to reader to direct the desktop computer to a website or app. Easy to use!
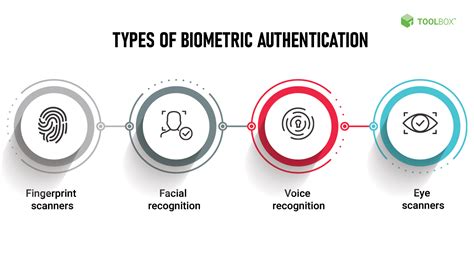
0 · types of fingerprint authentication
1 · types of data authentication
2 · types of authentication methods
3 · most secure authentication
4 · endpoint authentication types
5 · certificate based authentication
6 · 3 types of authentication
Auburn football kicks off its 2024 season four days from now vs. Alabama A&M, and the Tigers are looking to do so by flipping the switch from last season's sour ending.. The .
Type 2 – Something You Have – includes all items that are physical objects, such as keys, smart phones, smart cards, USB drives, and token devices. (A token device produces a time-based PIN or can compute a response from a challenge number issued by the server.). Something you know – Type 1 Authentication (passwords, pass phrase, PIN .
Two-Factor Authentication (2FA): Combining Type I (password) with Type II . Type 2 – Something You Have – includes all items that are physical objects, such as keys, smart phones, smart cards, USB drives, and token devices. (A token device produces a time-based PIN or can compute a response from a challenge number issued by the server.).
Something you know – Type 1 Authentication (passwords, pass phrase, PIN etc.). Something you have – Type 2 Authentication (ID, Passport, Smart Card, Token, cookie on PC etc.). Something you are – Type 3 Authentication (and Biometrics) (Fingerprint, Iris Scan, Facial geometry etc.). Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication.
Two-Factor Authentication (2FA): Combining Type I (password) with Type II (security token or mobile phone). Three-Factor Authentication: Combining Type I (password), Type II (smart card),. – The very basics. – Authentication with a smart card over mTLS. – Summary. – Further reading. Background and Scope. I have been working to document Certificate-Based Authentication (CBA) in Azure on desktop and mobile, but in doing so I realized two things:
Multi-factor authentication (MFA) is a layered approach to securing physical and logical access where a system requires a user to present a combination of two or more different authenticators to verify a user’s identity for login.
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.Also known as possession-based authentication, type 2 authentication is based on what the user has in possession like a security key, ID badge, memory card, or smart card token. On their own, possession-based factors are anything that users in their hands. A false rejection error (also called type 1 error) occurs when a system falsely rejects a known user and indicates the user is not known. A false acceptance error (also called a type 2 error) occurs when a system falsely identifies an unknown user as a known user.
Type 2 – Something You Have – includes all items that are physical objects, such as keys, smart phones, smart cards, USB drives, and token devices. (A token device produces a time-based PIN or can compute a response from a challenge number issued by the server.).
add custom nfc card to apple wallet
types of fingerprint authentication

Something you know – Type 1 Authentication (passwords, pass phrase, PIN etc.). Something you have – Type 2 Authentication (ID, Passport, Smart Card, Token, cookie on PC etc.). Something you are – Type 3 Authentication (and Biometrics) (Fingerprint, Iris Scan, Facial geometry etc.). Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication.
Two-Factor Authentication (2FA): Combining Type I (password) with Type II (security token or mobile phone). Three-Factor Authentication: Combining Type I (password), Type II (smart card),. – The very basics. – Authentication with a smart card over mTLS. – Summary. – Further reading. Background and Scope. I have been working to document Certificate-Based Authentication (CBA) in Azure on desktop and mobile, but in doing so I realized two things:Multi-factor authentication (MFA) is a layered approach to securing physical and logical access where a system requires a user to present a combination of two or more different authenticators to verify a user’s identity for login.
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.Also known as possession-based authentication, type 2 authentication is based on what the user has in possession like a security key, ID badge, memory card, or smart card token. On their own, possession-based factors are anything that users in their hands.
types of data authentication
card nfc for iphone

Live coverage of the Virginia Cavaliers vs. Notre Dame Fighting Irish NCAAF game on ESPN, including live score, highlights and updated stats.
authentication type smart card type 1 type 2|most secure authentication