rfid hacking connect card The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . Listen to radio stations from Auburn NY, from a wide variety of genres like Alternative, College, News and Talk. Enjoy stations such as Finger Lakes News Radio - WAUB, Win 89 FM - .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
The official source for NFL news, video highlights, fantasy football, game-day coverage, schedules, stats, scores and more. . 2009 — WILD CARD . Examining NFC playoff picture .1998–99 NFL playoffs; Dates: January 2–31, 1999: Season: 1998: Teams: 12: Games played: 11: . The Cardinals 9–7 record and Wild Card win in Dallas ultimately did not signal a turnaround for the long-troubled franchise. . This was the first NFC Championship Game to go to overtime (since, there have . See more
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low .
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and .

The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low .Flipper Zero can be used to perform security assessments on RFID and NFC systems, such as cloning RFID cards, sniffing NFC communications, and analyzing vulnerabilities in these .
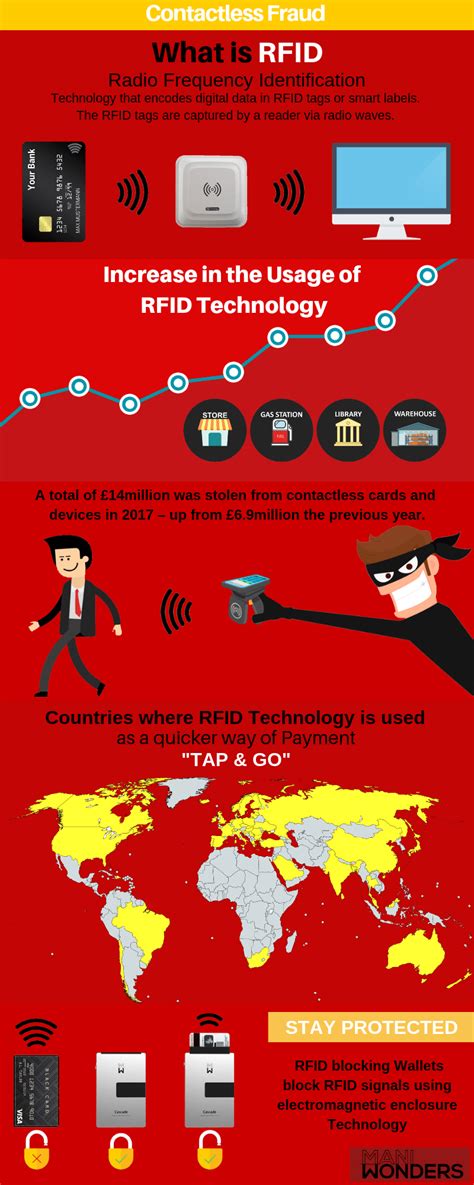
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
rfid scammers
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain .
This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the .How Can RFID Be Hacked? Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on .
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
RFID hacking refers to the unauthorized access or manipulation of RFID systems by exploiting their inherent vulnerabilities. There are several ways in which RFID hacking can occur: .
rfid scam
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and .
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low .Flipper Zero can be used to perform security assessments on RFID and NFC systems, such as cloning RFID cards, sniffing NFC communications, and analyzing vulnerabilities in these .
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain .This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the .
How Can RFID Be Hacked? Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on . Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
rfid how to block

do apps stay on smart phone when changing sim cards
does a smart card reader use flash memory
Auburn football kicks off its 2024 season four days from now vs. Alabama A&M, and the Tigers are looking to do so by flipping the switch from last season's sour ending.. The .
rfid hacking connect card|how to prevent rfid cloning