smart card for security scholarly articles The results suggest that usefulness, security, ease of use, awareness, support, visibility, image, trailibility, social norms and satisfaction are factors which have significant and . About this app. Join the future of networking with HiHello, the leading digital business card app trusted by professionals worldwide. With .
0 · Using a systematic framework to critically analyze proposed
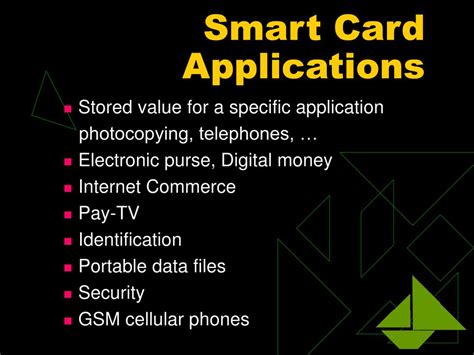
1 · Smart card applications and security
2 · Smart Card Security Model Based on Sensitive Information
3 · Smart Card Research and Advanced Applications
4 · Security, Privacy and Risks Within Smart Cities: Literature
5 · Security Evaluation of Smart Cards and Secure Tokens: Benefits
6 · Privacy
7 · Global Identification of Smart Card Technologies
8 · Full article: Privacy and biometrics for smart healthcare systems
9 · Appraising the Smart Card Technology Adoption; Case of
The #1 Smart Digital Name Card with integrated NFC, QR Code, CRM and analytics - trusted by 120K+ worldwide. Build networks, reduce waste and make an impact.
ProVerif is an automatic cryptographic protocol verifier, which can model many symmetric and asymmetric public-key cryptographic primitives as rewrite rules or equations, including encryptions, signatures, hash functions, and Diffie-Hellman key agreements.” Firstly, a communication channel between the user . See more
The proposed proposal provides biometric template privacy protection, and achieves mutual authentication, user anonymity and untraceability. See moreIn this part, we give a particular careful comparison of our PSBA protocol, Das et al.’s and Al-Saggaf et al.’s proposal. They are also biometric-based user . See more The results suggest that usefulness, security, ease of use, awareness, support, visibility, image, trailibility, social norms and satisfaction are factors which have significant and . The importance of smart card based two factor authentication can be gauged by the fact that many schemes have been proposed so far yet none of them used a systematic .
By using data collected from 398 individuals living in Spain and using Partial Least Square (PLS) analysis, it was found that security has a significant effect on continuance . Smart card technology is currently popular for global identification. The use of smart cards continues to increase in various fields along with the rapid development of technology. .
The 12 full papers presented in this volume were carefully reviewed and selected from 26 submissions. They were organized in topical sections named: post-quantum cryptography; efficient implementations; and physical attacks. This research aims to leverage findings and assumptions made from the previous report to determine the security benefits and drawbacks of a smart card- based hardware root .
In this paper, we presented different forms of biometric factors and technologies and their applications in the smart healthcare system to enhance security and privacy in relation to .
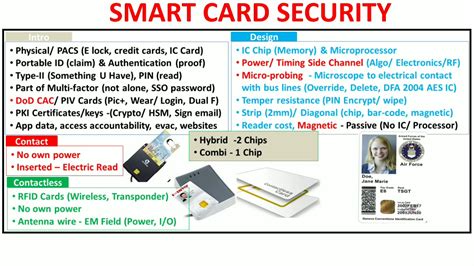
1 Citations. Abstract. Systems for important and sensitive data increasingly use smart cards, especially in large companies and institutions, such as bank cards, access . This article gives brief introduction to the security mechanisms used in smart card technology. Firstly we introduce the properties of contact and contactless smart cards; then we . Furthermore, we put forth a privacy-aware smart card based biometric authentication (PSBA) scheme for e-health, which provides more desired security properties .
The results suggest that usefulness, security, ease of use, awareness, support, visibility, image, trailibility, social norms and satisfaction are factors which have significant and . The importance of smart card based two factor authentication can be gauged by the fact that many schemes have been proposed so far yet none of them used a systematic . By using data collected from 398 individuals living in Spain and using Partial Least Square (PLS) analysis, it was found that security has a significant effect on continuance . Smart card technology is currently popular for global identification. The use of smart cards continues to increase in various fields along with the rapid development of technology. .
The 12 full papers presented in this volume were carefully reviewed and selected from 26 submissions. They were organized in topical sections named: post-quantum cryptography; . This research aims to leverage findings and assumptions made from the previous report to determine the security benefits and drawbacks of a smart card- based hardware root . In this paper, we presented different forms of biometric factors and technologies and their applications in the smart healthcare system to enhance security and privacy in relation to . 1 Citations. Abstract. Systems for important and sensitive data increasingly use smart cards, especially in large companies and institutions, such as bank cards, access .
This article gives brief introduction to the security mechanisms used in smart card technology. Firstly we introduce the properties of contact and contactless smart cards; then we . Furthermore, we put forth a privacy-aware smart card based biometric authentication (PSBA) scheme for e-health, which provides more desired security properties .
The results suggest that usefulness, security, ease of use, awareness, support, visibility, image, trailibility, social norms and satisfaction are factors which have significant and . The importance of smart card based two factor authentication can be gauged by the fact that many schemes have been proposed so far yet none of them used a systematic . By using data collected from 398 individuals living in Spain and using Partial Least Square (PLS) analysis, it was found that security has a significant effect on continuance . Smart card technology is currently popular for global identification. The use of smart cards continues to increase in various fields along with the rapid development of technology. .
The 12 full papers presented in this volume were carefully reviewed and selected from 26 submissions. They were organized in topical sections named: post-quantum cryptography; .
Using a systematic framework to critically analyze proposed
This research aims to leverage findings and assumptions made from the previous report to determine the security benefits and drawbacks of a smart card- based hardware root . In this paper, we presented different forms of biometric factors and technologies and their applications in the smart healthcare system to enhance security and privacy in relation to .
1 Citations. Abstract. Systems for important and sensitive data increasingly use smart cards, especially in large companies and institutions, such as bank cards, access .
how to login to windows 7 with smart card

Some are made for reading and writing NFC tags, while others perform specific tasks like unlocking your smartphone, setting up a smart alarm, sharing WiFi, etc. In this article, we’ll take a look at some of the best NFC apps for Android. Let’s begin.
smart card for security scholarly articles|Security, Privacy and Risks Within Smart Cities: Literature