how smart card works authentication Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
Animal Crossing Happy Home Designer Nintendo 3ds NFC Reader / Writer Set. .
0 · yubikey vs smart card
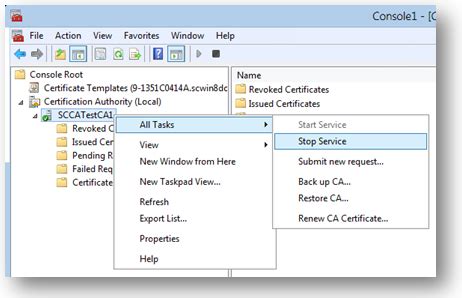
1 · windows 10 smart card setup
2 · smart card yubikey
3 · smart card based authentication
4 · smart card authentication windows
5 · read smart card windows 10
6 · how does cac authentication work
7 · enable smart card log on
NFC stands for Near-field communication. See more
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.
Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in with a Windows domain account. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
Smart cards provide an easy and movable way to prove who you are, without needing to remember hard passwords. Smart card security can be combined with other authentication methods like personal identification numbers or biometrics for stronger protection. Implementing Smart Card Authentication: Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
A user usually connects a smart card with a computer and specific software on the computer interacts with the smart card and uses the cryptographic keys stored on the smart card to authenticate a user. How does smart card authentication work? And, why is it considered more secure? In this article, we would discuss that in detail.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
How does smart card authentication work? Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is either contact or contactless smart card readers.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software. Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in with a Windows domain account.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.

dell smart card reader keyboard driver
yubikey vs smart card
Smart cards provide an easy and movable way to prove who you are, without needing to remember hard passwords. Smart card security can be combined with other authentication methods like personal identification numbers or biometrics for stronger protection. Implementing Smart Card Authentication: Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
A user usually connects a smart card with a computer and specific software on the computer interacts with the smart card and uses the cryptographic keys stored on the smart card to authenticate a user. How does smart card authentication work? And, why is it considered more secure? In this article, we would discuss that in detail.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
windows 10 smart card setup
enable smart card logon windows 10

I find having an official Pro Controller is a much better option for having basically an external Amiibo reader than the Joycons. Sure, they can also drift, but it's a significantly lesser issue .
how smart card works authentication|smart card based authentication