list some of the security concerns of an rfid system In a spoofing attack, the attacker masquerade as a legitimate user of the system. The attacker can pose himself as an authorized Object Naming Service user or database user. If an attacker can successfully get access to the system with his spoofed . See more The nfcTube card has a NFC chip inside that wirelessly sends your information to the phone. If .Load NFC Cards: Place the NFC cards into the printer’s input tray or designated card slot. Make sure that the cards are correctly aligned and securely positioned to avoid any printing errors or misalignments. 4. Set .
0 · rfid security problems
1 · rfid privacy and security issues
2 · rfid is vulnerable to
3 · rfid disadvantages
4 · problems with rfid technology
5 · problems with rfid
6 · is rfid dangerous
7 · compliance issues with rfid bands
A place to talk about everything that you can add to your Apple Wallet, Notably .
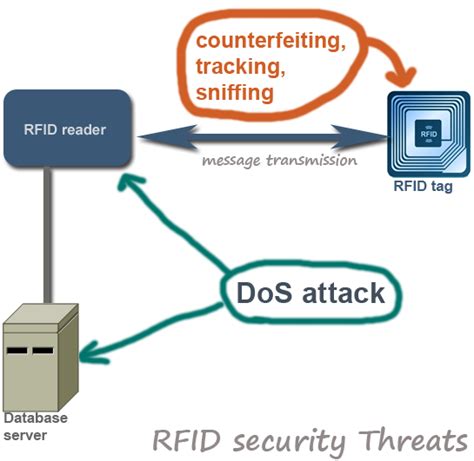
Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID related security issues. Like any other . See moreRFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: See more
In a spoofing attack, the attacker masquerade as a legitimate user of the system. The attacker can pose himself as an authorized Object Naming Service user or database user. If an attacker can successfully get access to the system with his spoofed . See moreIn this type of attack, an attacker tries to insert system commands to the RFID system instead of sending normal data.an example of RFID insert attack is that a tag carrying system . See moreAs you know that repudiation means when as user officially deny that he has done an action and we have no way to verify that whether he has performed that particular action. In the case of . See morecurrent RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this .
rfid security problems
Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several .
rfid chip acceptor
current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this . Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; .
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack . Part 2 examines some of the more common security and privacy concerns associated with RFID, primarily related to retail and consumer applications. What is RFID? This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .
“Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and . RFID systems are vulnerable to denial of service (DoS) attacks by disrupting communication between tags and readers. Malicious actors overwhelm these two with .However, RFID systems also raise serious privacy and security concerns. This article offers a brief review of the main threats to RFID systems and proposes a methodology for qualitatively . Within less than a decade, a large number of research papers dealing with security issues of RFID technology have appeared. In this paper we want to provide some thoughts on .
Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several .current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this . Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; .
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack . Part 2 examines some of the more common security and privacy concerns associated with RFID, primarily related to retail and consumer applications. What is RFID?
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world . “Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and . RFID systems are vulnerable to denial of service (DoS) attacks by disrupting communication between tags and readers. Malicious actors overwhelm these two with .However, RFID systems also raise serious privacy and security concerns. This article offers a brief review of the main threats to RFID systems and proposes a methodology for qualitatively .
Try the phone App first to get the hang of it. Easier for testing and understanding the whole process. You create your record in the "Write" section, then you write your record, approach .Pixel 9 Studio. 1 167. SQR NEO - NFC Business Cards. SQR NEO - Smart Business Cards. 1 44. NFC Cards Bauernwirt. Paolo Reininghaus. 2 42. Upgrade to Behance Pro today: Get advanced analytics, a custom portfolio website, .
list some of the security concerns of an rfid system|problems with rfid technology