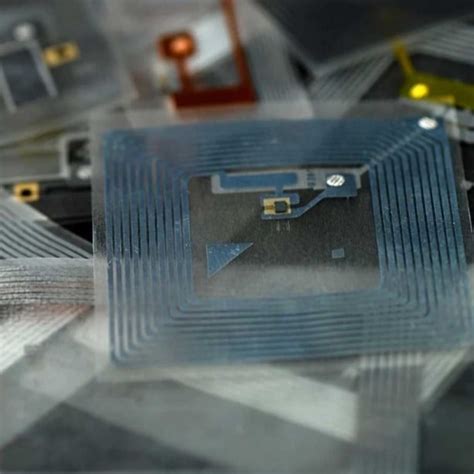
destruction of rfid tags Physical destruction is one of the most straightforward methods to disable an RFID chip. By physically damaging the chip itself, you can render it non-functional and prevent it from transmitting or receiving data. Download the NFC app and make the settings as described above. Format 3 or 4 tags. Write the tags as described above, Put "Attendance" as the shortcut, (make sure there are no spaces after the word Attendance), and a First and Last .Begin building your tag reader by configuring your app to detect NFC tags. Turn on Near Field Communication Tag Reading under the Capabilities tab for the project’s target (see Add a capability to a target). This step: Adds the NFC tag-reading feature to the App ID. Adds the .
0 · rfid chip deactivation
1 · rfid chip breakdown
2 · how to disable rfid
3 · how to disable a rfid chip
4 · can rfid tag break down
To proceed simply press the Volume Down and Power buttons together for around 10 seconds until the phone restarts. If your problem persists please check that the correct .
An attacker uses methods to deactivate a passive RFID tag for the purpose of rendering the tag, badge, card, or object containing the tag unresponsive. RFID tags are used primarily for .

scanner guard rfid does it work
One thing that could damage a tag is high heat, which can melt the solder connecting the antenna to the chip. Solder typically melts at 183 degrees Celsius (361 degrees Fahrenheit).An attacker uses methods to deactivate a passive RFID tag for the purpose of rendering the tag, badge, card, or object containing the tag unresponsive. RFID tags are used primarily for access control, inventory, or anti-theft devices.RFID label collision refers to when multiple RFID labels communicate with an RFID reader at the same time, and signal interference occurs, resulting in reading failure or misreading. Label collisions can affect system performance and reduce data transmission efficiency.
rfid chip deactivation
Physical destruction is one of the most straightforward methods to disable an RFID chip. By physically damaging the chip itself, you can render it non-functional and prevent it from transmitting or receiving data. Overview. Introduction to RFID and its applications. Types of security attacks to Passive RFID Tags. Impersonation. Information Leakage. Physical Manipulation. Types of Protection Methods for RFID Tags. PUFs and Unclonable RFID Tags. Other means of security. Fingerprinting RFID Tags. References. RFID.
Innovative Ways to Reuse RFID Tags. Given the vast array of applications for RFID tags, there are almost no limits to how they can be reused. Tags can even transcend industries. They could pass, for instance, from logistics to an entirely different field, like pharmaceuticals. Reusing RFID Tags. Reusing RFID tags can significantly reduce electronic waste and promote sustainable practices. While some RFID tags are designed for a single-use purpose, many can be reprogrammed and reused multiple times as they come with a read-write function and can be rewritten with new information. Abstract. Although Radio Frequency Identification (RFID) is poised to displace barcodes, security vulnerabilities pose serious challenges for global adoption of the RFID technology. Specifically, RFID tags are prone to basic cloning and counterfeiting security attacks. Though they sound highly technical—and thus expensive—RFID tags run between a few cents to a few dollars per chip depending on the specs. And, with up to 90% of retailers using RFID technology, the chips are widespread and easy to access.. To Bhat and Bharadia, who is also a faculty member of the UC San Diego Center for Wireless Communications, these .
rfid chip breakdown
how to disable rfid
The global RFID market in 2023 was estimated at billion, with the retail segment representing the largest portion of this total market at 30 percent, or approximately .2 billion.

One thing that could damage a tag is high heat, which can melt the solder connecting the antenna to the chip. Solder typically melts at 183 degrees Celsius (361 degrees Fahrenheit).
An attacker uses methods to deactivate a passive RFID tag for the purpose of rendering the tag, badge, card, or object containing the tag unresponsive. RFID tags are used primarily for access control, inventory, or anti-theft devices.
RFID label collision refers to when multiple RFID labels communicate with an RFID reader at the same time, and signal interference occurs, resulting in reading failure or misreading. Label collisions can affect system performance and reduce data transmission efficiency. Physical destruction is one of the most straightforward methods to disable an RFID chip. By physically damaging the chip itself, you can render it non-functional and prevent it from transmitting or receiving data. Overview. Introduction to RFID and its applications. Types of security attacks to Passive RFID Tags. Impersonation. Information Leakage. Physical Manipulation. Types of Protection Methods for RFID Tags. PUFs and Unclonable RFID Tags. Other means of security. Fingerprinting RFID Tags. References. RFID. Innovative Ways to Reuse RFID Tags. Given the vast array of applications for RFID tags, there are almost no limits to how they can be reused. Tags can even transcend industries. They could pass, for instance, from logistics to an entirely different field, like pharmaceuticals.
Reusing RFID Tags. Reusing RFID tags can significantly reduce electronic waste and promote sustainable practices. While some RFID tags are designed for a single-use purpose, many can be reprogrammed and reused multiple times as they come with a read-write function and can be rewritten with new information. Abstract. Although Radio Frequency Identification (RFID) is poised to displace barcodes, security vulnerabilities pose serious challenges for global adoption of the RFID technology. Specifically, RFID tags are prone to basic cloning and counterfeiting security attacks.
Though they sound highly technical—and thus expensive—RFID tags run between a few cents to a few dollars per chip depending on the specs. And, with up to 90% of retailers using RFID technology, the chips are widespread and easy to access.. To Bhat and Bharadia, who is also a faculty member of the UC San Diego Center for Wireless Communications, these .
how to disable a rfid chip
can rfid tag break down
Gemalto IDBridge CT31 PIV USB smartcard reader. A contemporary, transparent ISO7816 .
destruction of rfid tags|can rfid tag break down