smart cards tokens security and applications pdf A step-by-step approach educates the reader in card types, production, operating systems, . Choose Register amiibo and follow the on-screen prompts to register the NFC cards. Place the NFC card on the NFC scanning area when prompted by the console. Step 4: Using NFC Cards on the Nintendo Switch. .
0 · what is smart card number
1 · what is smart card authentication
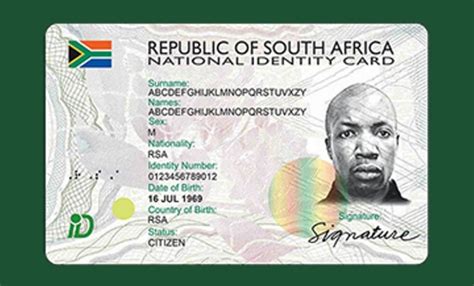
2 · smart card identity
3 · smart card identification
4 · smart card based identification system
5 · smart card based authentication
6 · memory based smart card
7 · azure smart card authentication
Security. NFC payments are generally considered secure. They often incorporate encryption to protect sensitive information such as credit card numbers. Additionally, many smartphones require authentication (such as a .NFC, which is short for near-field communication, is a technology that allows devices like phones and smartwatches to exchange small bits of data with other devices and read NFC-equipped cards over relatively short distances. The technology behind NFC is very similar to radio-frequency identification . See more
what is smart card number
rfid-enabled food safety and traceability systems
what is smart card authentication
A step-by-step approach educates the reader in card types, production, operating systems, .presents the main features of smart card technology in the light of the EMV card specificati. This state-of-the art work combines a cross-discipline overview of smart cards, .
presents the main features of smart card technology in the light of the EMV card . A step-by-step approach educates the reader in card types, production, .A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.

This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication.
rfid solutions for warehouse management rfid systems datexdatex
A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.Chapter 9: “Smart Card Security” gives a very good introduction of the different types of attacks that may apply to smart cards. It briefly describes invasive attacks. The focus is on semi-invasive and non-invasive attacks. He presents the different categories of side channel attacks. The author clearly likes thepresents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. This chapter provides a first introduction to a wide range of smart cards and tokens, considering the various types, capabilities, popular applications and the practicality of their.

A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development,. This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.Smart Cards, Tokens, Security and Applications. This book provides a broad overview of the many card systems and solutions that are in practical use today. This new edition adds content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking or payment cards, identity cards and passports, mobile systems .
A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.
This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.
presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication.
A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.
Chapter 9: “Smart Card Security” gives a very good introduction of the different types of attacks that may apply to smart cards. It briefly describes invasive attacks. The focus is on semi-invasive and non-invasive attacks. He presents the different categories of side channel attacks. The author clearly likes thepresents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. This chapter provides a first introduction to a wide range of smart cards and tokens, considering the various types, capabilities, popular applications and the practicality of their. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development,.
This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.
2. Launch 'Samsung Wallet' > Click 'All' on the bottom right > Samsung Pass You can enjoy .
smart cards tokens security and applications pdf|memory based smart card