pki smart card authentication If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware. NFC tags are passive, meaning they don't have any power source. Instead, they literally draw power from the device that reads them, thanks to .
0 · smart card two factor authentication
1 · smart card computer access
2 · smart card authentication step by
3 · pki smarttoken
4 · manage smart cards
5 · fips 140 2 smart card
6 · authentication smart card
7 · adfs smart card authentication
Step 1. Go to Settings > Connections > NFC and contactless payments. Step 2. Tap Contactless payments, and then select your preferred payment app. * Image shown is for illustration purposes only. Step 3. Additional payment apps can .
Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a traditional credit card form factor, enabling organizations to address their PKI security needs.

The Smart Card Technical Reference describes the Windows smart card infrastructure for physical smart cards and how smart card-related components work in Windows. This document also contains information about tools that information technology (IT) developers and administrators can . See more If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.
Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a traditional credit card form factor, enabling organizations to address their PKI security needs.
How to Configure a PKI Smart Card for 802.1x Authentication. There’s no single process that can configure every smart card for 802.1x authentication since there are many manufacturers and many different devices that smart cards can be found in. Learn how Adaptive Multi-Factor Authentication combats data breaches, weak passwords, and phishing attacks. PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke .To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.
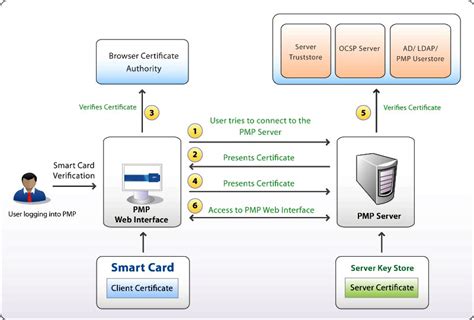
6.1. Creating local certificates. Copy link. Follow this procedure to perform the following tasks: Generate the OpenSSL certificate authority. Create a certificate signing request. Warning. The following steps are intended for testing purposes only. PKI fundamentals are crucial to exploiting the capabilities of the Internet securely. Discover how PKI enables the verification of identities to securely exchange data over both public and private networks. In this post, we will walk through step-by-step how you can set up and configure new or existing Microsoft PKI to support PIV smart card authentication including setting up an OCSP responder, proper configuration of Active Directory, domain controllers, certificate templates, group policy, and WorkSpaces.
Enable smart card or USB tokens to authenticate users and securely access domains, networks and VDI environments. End manual identity management with automated provisioning through a Group Policy Object (GPO), AD group memberships, PKI Enterprise Gateway and the PKI client.To authenticate a user who logs in with a smart card, the appliance has to determine the revocation status of the user certificate. Configuring certificate validation is a prerequisite for enabling smart card authentication. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.Thales's portfolio of certificate-based smart cards offers strong multi-factor authentication in a traditional credit card form factor, enabling organizations to address their PKI security needs.
How to Configure a PKI Smart Card for 802.1x Authentication. There’s no single process that can configure every smart card for 802.1x authentication since there are many manufacturers and many different devices that smart cards can be found in. Learn how Adaptive Multi-Factor Authentication combats data breaches, weak passwords, and phishing attacks. PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke .
smart card two factor authentication
To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.6.1. Creating local certificates. Copy link. Follow this procedure to perform the following tasks: Generate the OpenSSL certificate authority. Create a certificate signing request. Warning. The following steps are intended for testing purposes only. PKI fundamentals are crucial to exploiting the capabilities of the Internet securely. Discover how PKI enables the verification of identities to securely exchange data over both public and private networks. In this post, we will walk through step-by-step how you can set up and configure new or existing Microsoft PKI to support PIV smart card authentication including setting up an OCSP responder, proper configuration of Active Directory, domain controllers, certificate templates, group policy, and WorkSpaces.
rfid card protectors
Enable smart card or USB tokens to authenticate users and securely access domains, networks and VDI environments. End manual identity management with automated provisioning through a Group Policy Object (GPO), AD group memberships, PKI Enterprise Gateway and the PKI client.
can a phone read rfid
smart card computer access

smart card authentication step by
Power up the Nintendo NFC Reader/Writer and make sure that the system and the .
pki smart card authentication|fips 140 2 smart card