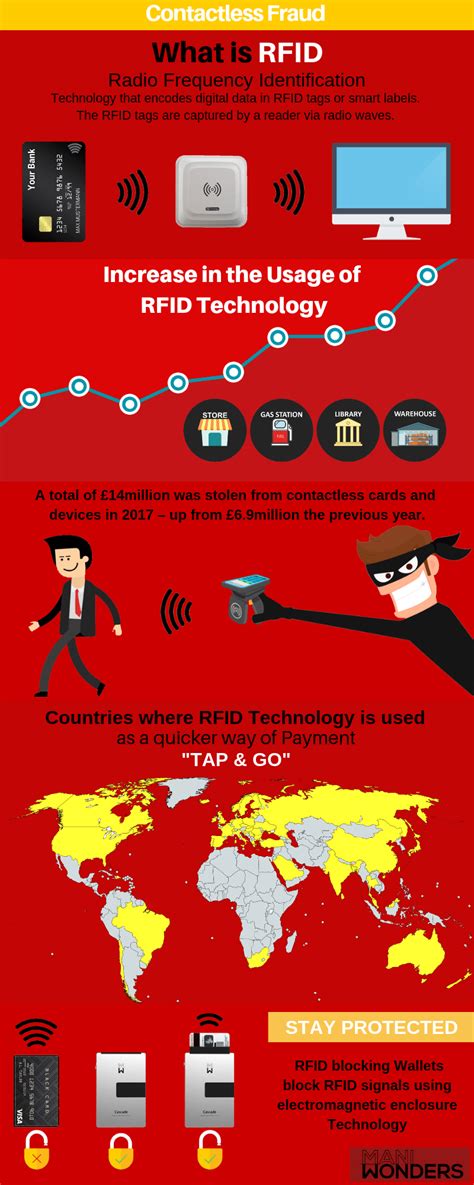
hacking rfid chips RFID stands for Radio Frequency Identification and it's used for short-distance communication of information. It does not require line of sight to work, meaning that the RFID chip and the reader merely need to be within range of each other to communicate. There are a few main types of RFID chip: 1. . See more ShopeePay. Step 1: Open the Shopee app, go to the ‘Me’ section, click on ShopeePay under ‘My Wallet’. Step 2: On the ShopeePay page, click ‘Load, Bills & Travel’, then under the Travel category, choose ‘BEEP CARD’. Step 3: .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Anyways, I've been making my own nfc cards but none of them will work on the switch version .
rfid scammers
RFID stands for Radio Frequency Identification and it's used for short-distance communication of information. It does not require line of sight to work, meaning that the RFID chip and the reader merely need to be within range of each other to communicate. There are a few main types of RFID chip: 1. . See moreRFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their . See moreAs hackers have demonstrated, RFID is not impervious from attacks. There are cheap ways to build a scanner, at which point they can scan tags for sensitive information. While the panic around this form of attack may outshadow the actual chance that you'll . See moreSo, if you do want to stay on the safe side, how do you block RFID signals? In general, metal and water are the best ways to block radio . See more
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or .
em 18 rfid reader
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala. MIFARE chips represent approximately 80% of the RFID passive tags in the world. Think of MIFARE as being the most used type of RFID tags. NFC is simply a newer technology to interact with the first two. With that little bit of knowledge, let’s focus on MIFARE.By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .

Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a device is performing a cryptographic operation, in order to extract its cryptographic key.
What is RFID Hacking And Seven Ways To Prevent It. RFID stands for Radio Frequency Identification, and it is a form of short-range communication between RFID-enabled . What is RFID hacking, and how can it be prevented in 7 ways? Radio Frequency Identification, or RFID, is a method of close-quarters communication between RFID-enabled readers and RFID-enabled data chips, such as those found in credit cards or staff ID badges (like electronic access control for doors or credit card readers).Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data. RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or .
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.
MIFARE chips represent approximately 80% of the RFID passive tags in the world. Think of MIFARE as being the most used type of RFID tags. NFC is simply a newer technology to interact with the first two. With that little bit of knowledge, let’s focus on MIFARE.By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from . Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms.
rfid scam
Researchers have designed an RFID chip that prevents so-called side-channel attacks, which analyze patterns of memory access or fluctuations in power usage when a device is performing a cryptographic operation, in order to extract its cryptographic key. What is RFID Hacking And Seven Ways To Prevent It. RFID stands for Radio Frequency Identification, and it is a form of short-range communication between RFID-enabled .
What is RFID hacking, and how can it be prevented in 7 ways? Radio Frequency Identification, or RFID, is a method of close-quarters communication between RFID-enabled readers and RFID-enabled data chips, such as those found in credit cards or staff ID badges (like electronic access control for doors or credit card readers).
rfid how to block
rfid hacking tool
The biggest roadblock here is, that most unis use their student IDs to open doors and record attendance. They do this via NFC of course. The way to replicate this would be HCE (Host .
hacking rfid chips|rfid how to block