smart card for authentication Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem . For best results, hold your card within an inch or two of the contactless symbol on the terminal (four rounded vertical lines similar to a Wi-Fi signal on its side). Or there could be problems with your card, such as: Your .
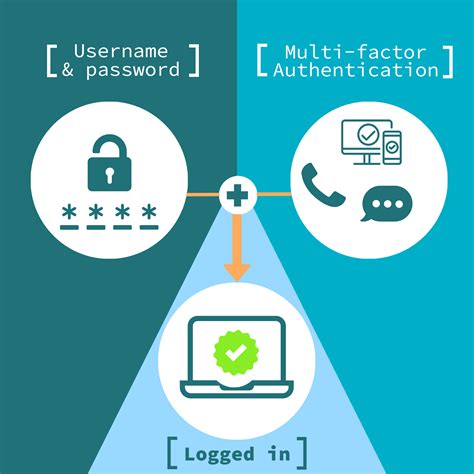
0 · smart card multi factor authentication
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
Create Customized Smart Metal NFC Card Add Name - Suit Up ( For Android Phones Only) Step into the future of networking with Nutcase Personalized NFC Cards. Designed for efficiency and elegance, these cards revolutionize how .NFC is a newer, high-frequency version of RFID, and also involves both tags and readers. NFC's higher frequency means that, while it can .
Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem .Learn how to use smart cards and smart card readers for authentication and remote desktop connections in Windows. Find out the requirements, services, and policies for smart card technologies.
Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem architecture.Learn what a Personal Identity Verification (PIV) credential is, who is eligible for it, and how it is used for logical and physical access to federal systems and facilities. Find out the standards, features, and benefits of PIV credentials and how to test them. Learn how to use smart cards for authentication, digital signatures, and key exchange in Windows. This document covers smart card architecture, certificate requirements, tools, settings, and troubleshooting.
Smart Card Authentication is a type of authentication that uses a physical card with a chip and a reader to verify users into enterprise resources. It is secure but expensive and requires hardware and software support.A smart card is a physical card with an embedded chip that acts as a security token. Learn how smart card authentication works, its benefits and drawbacks, and how to use it with YubiKey. Learn how smart cards use embedded chips to verify identity and perform secure transactions. Explore the types, components, protocols, and advantages of smart card authentication, as well as the common challenges and limitations.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data. Learn how smart card authentication works, how to implement it, and what best practices to follow. Smart card authentication is a secure and convenient way to verify identity using a smart card with a microchip and a card reader.
Learn how to use smart cards and smart card readers for authentication and remote desktop connections in Windows. Find out the requirements, services, and policies for smart card technologies. Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem architecture.Learn what a Personal Identity Verification (PIV) credential is, who is eligible for it, and how it is used for logical and physical access to federal systems and facilities. Find out the standards, features, and benefits of PIV credentials and how to test them.
Learn how to use smart cards for authentication, digital signatures, and key exchange in Windows. This document covers smart card architecture, certificate requirements, tools, settings, and troubleshooting.Smart Card Authentication is a type of authentication that uses a physical card with a chip and a reader to verify users into enterprise resources. It is secure but expensive and requires hardware and software support.
A smart card is a physical card with an embedded chip that acts as a security token. Learn how smart card authentication works, its benefits and drawbacks, and how to use it with YubiKey. Learn how smart cards use embedded chips to verify identity and perform secure transactions. Explore the types, components, protocols, and advantages of smart card authentication, as well as the common challenges and limitations.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
smart card multi factor authentication
Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data.
allflex rfid ear tags
smart card identity
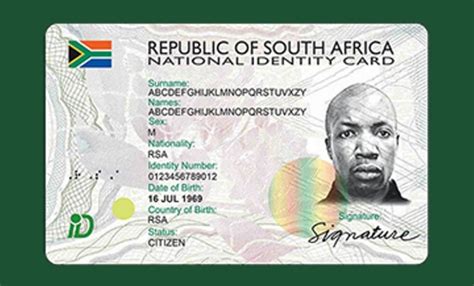
smart card based identification system
IOS gives two (three) solutions to NFC passes: HCE - limited solely to Apple VAS protocol. .Introducing VistaConnect – a free service that adds an online extension to a single business card you keep. Smart scanning technology instantly brings customers to schedules, signup forms and everything else that makes your business go. See our guide. See more
smart card for authentication|smart card identity