using smart card for authentication In summary, smart card authentication provides a complete solution for making security better and organizing entry control nowadays. Using smart cards’ advanced secret techniques, groups can require strong proof policies, shield touchy data, and lessen the danger of information rupture. Stay up to date with your favorite team to see if they have a chance to make the 2024 playoffs. Seven teams from each conference will make it to the postseason. Check out which teams are .
0 · smart card multi factor authentication
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
After Canon PRINT Inkjet / SELPHY has been installed, open it. Tap the icon at the upper left. Place your Android device on the NFC symbol on the printer. The device will then communicate with the printer. You will be asked to register the .
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
In summary, smart card authentication provides a complete solution for making security better and organizing entry control nowadays. Using smart cards’ advanced secret techniques, groups can require strong proof policies, shield touchy data, and lessen the danger of information rupture.
If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.
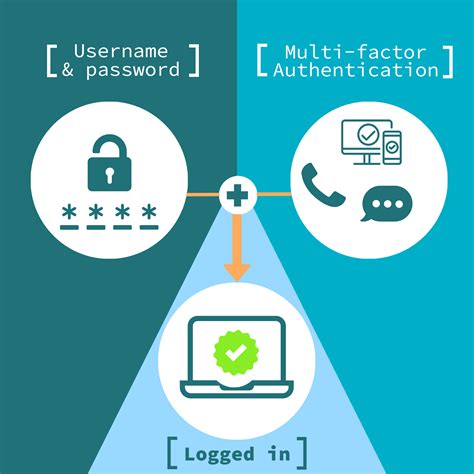
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.How does smart card authentication work? Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is either contact or contactless smart card readers. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data. Smart card authentication is a two-step login process that uses a smart card. The smart card stores a user’s public key credentials and a personal identification number (PIN), which acts as the secret key to authenticate the user to the smart card.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. In summary, smart card authentication provides a complete solution for making security better and organizing entry control nowadays. Using smart cards’ advanced secret techniques, groups can require strong proof policies, shield touchy data, and lessen the danger of information rupture. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.
driving licence smart card reader
How does smart card authentication work? Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is either contact or contactless smart card readers.
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.Smart card authentication is an important part of cybersecurity, providing an extra layer of protection in our increasingly digital world. It involves the use of smart cards, which are small, pocket-sized cards with embedded integrated circuits or "chips" that can process data.
smart card multi factor authentication
smart card identity
smart card based identification system
Samsung Wallet uses NFC (Near Field Communication) technology to transfer card information to any NFC-enabled (tap and pay) payment terminal. Instead of tapping your debit or credit card, hold the .
using smart card for authentication|smart card based identification system