rfid reader hack Flipper Zero is a portable multi-tool for pentesters and geeks in a toy-like body. It loves hacking digital stuff, such as radio protocols, access control systems, hardware, and more. It's fully open-source and customizable, so you can extend it in whatever way you like. According to Elavon, the company that supports NFC technology for Regions Bank merchant customers, contactless payments have grown by 150% in the U.S. since 2019. According to a .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
Check out our nfc epoxy card selection for the very best in unique or custom, handmade pieces .Cardless ATM access allows customers to access Chase ATMs using an eligible Chase debit card that has been loaded into an Apple Pay, Google Wallet ™ or Samsung Pay mobile wallet. Once you have successfully loaded your card .
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC .Flipper Zero is a portable multi-tool for pentesters and geeks in a toy-like body. It loves hacking . The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.
Flipper Zero is a portable multi-tool for pentesters and geeks in a toy-like body. It loves hacking digital stuff, such as radio protocols, access control systems, hardware, and more. It's fully open-source and customizable, so you can extend it in whatever way you like.
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.November 3, 2013. Security researcher [Fran Brown] sent us this tip about his Tastic RFID Thief, which can stealthily snag the information off an RFID card at long range. If you’ve worked. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.
Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.BambuLab printers use MiFare 13.56MHZ RFID tags. These tags contain a unique ID that is not encrypted (called the UID) In most cases UID is fixed (not-changable). Some "hackable" rfid tags allow you to set the UID to anything you want. Blocks (Encrypted) MiFare tags also contain "Blocks" of data. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
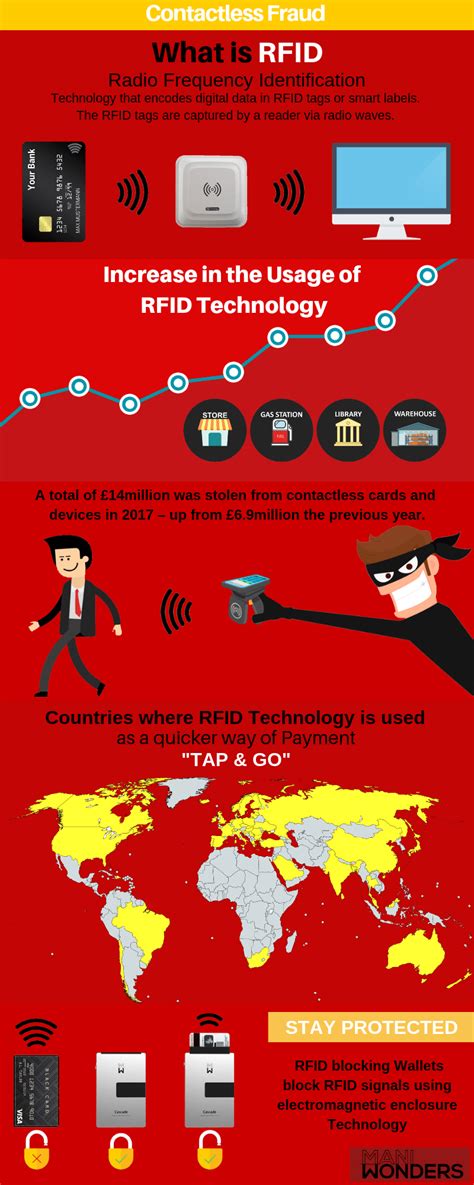
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
rfid scammers

The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.Flipper Zero is a portable multi-tool for pentesters and geeks in a toy-like body. It loves hacking digital stuff, such as radio protocols, access control systems, hardware, and more. It's fully open-source and customizable, so you can extend it in whatever way you like.
program nfc tag ios
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.November 3, 2013. Security researcher [Fran Brown] sent us this tip about his Tastic RFID Thief, which can stealthily snag the information off an RFID card at long range. If you’ve worked. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.
Common RFID hacking techniques include RFID signal interception, tag cloning, replay attacks, brute-forcing cryptographic keys, signal jamming, and exploiting weak encryption or authentication mechanisms. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.BambuLab printers use MiFare 13.56MHZ RFID tags. These tags contain a unique ID that is not encrypted (called the UID) In most cases UID is fixed (not-changable). Some "hackable" rfid tags allow you to set the UID to anything you want. Blocks (Encrypted) MiFare tags also contain "Blocks" of data.
rfid scam
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
rfid how to block


no supported nfc for this tag
passive nfc ear tag herddogg
AFC (1) Dolphins receive a bye (2) Ravens vs. (7) Texans (3) Chiefs vs. (6) Colts (4) Jaguars vs. (5) Browns NFC (1) Eagles receive a bye (2) 49ers vs. (7) Packers (3) Lions vs. (6) Vikings . See more
rfid reader hack|is rfid safe to hack