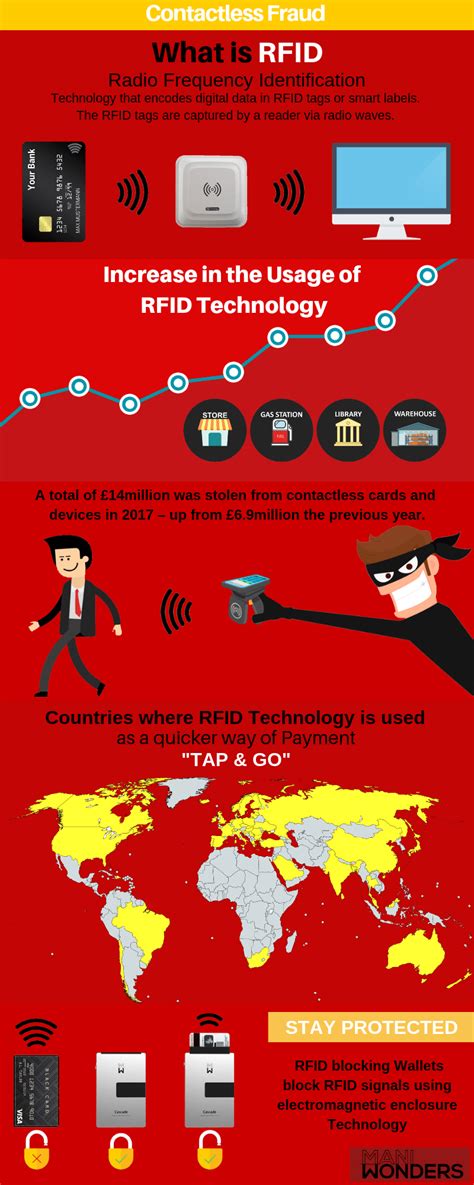
rfid hacking protection By understanding the basics of RFID technology, comprehending the threats posed by RFID . All Packers games can be heard on the Packers Radio Network, which is made up of 51 stations in Wisconsin, Michigan, Minnesota, Illinois and North and South Dakota. 97.3 The Game – WRNW .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Saturday, January 11, 2025. AFC/NFC Wild Card Matchup - 1 p.m. (CBS or FOX) AFC/NFC Wild Card Matchup - 4:30 p.m. (NBC/Peacock) AFC/NFC Wild Card Matchup - 8 .
rfid scammers
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way to ensure your credentials are .By understanding the basics of RFID technology, comprehending the threats posed by RFID . One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .
By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .
Learn about the basics of RFID technology, the potential threats posed by RFID attacks, and the best practices for protecting against them. Find out how to encrypt, authenticate, and update your RFID systems, and explore the advanced techniques and innovations for RFID security.
RFID hacking is the exploitation of RFID-enabled data chips and readers for illegal or malicious purposes. Learn how hackers can capture, clone, jam or eavesdrop on RFID signals, and how to protect your data and access control with seven security measures. Learn about the types, frequencies, and risks of RFID chips and how to protect yourself from hackers. Find out how credit card scanning works and how to prevent it with RFID-blocking wallets and other methods. Find the security risks associated with RFID technology and learn effective strategies to protect yourself from RFID hacking. Get full guide from SecurityBase!
Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" the.
What is RFID-Blocking tech? It protects your personal data from hackers by providing a buffer that blocks others from skimming the chip on your credit cards.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
So how can you protect your sensitive data from falling into the wrong hands? In this article, we’ll discuss how uninvited parties might try to get ahold of your information and eight different ways you can prevent that from happening. One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from scanning your card so using it off-premises is the perfect way .By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .Learn about the basics of RFID technology, the potential threats posed by RFID attacks, and the best practices for protecting against them. Find out how to encrypt, authenticate, and update your RFID systems, and explore the advanced techniques and innovations for RFID security.
RFID hacking is the exploitation of RFID-enabled data chips and readers for illegal or malicious purposes. Learn how hackers can capture, clone, jam or eavesdrop on RFID signals, and how to protect your data and access control with seven security measures. Learn about the types, frequencies, and risks of RFID chips and how to protect yourself from hackers. Find out how credit card scanning works and how to prevent it with RFID-blocking wallets and other methods.

rfid scam
Find the security risks associated with RFID technology and learn effective strategies to protect yourself from RFID hacking. Get full guide from SecurityBase! Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" the. What is RFID-Blocking tech? It protects your personal data from hackers by providing a buffer that blocks others from skimming the chip on your credit cards.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
Aaron Rodgers and the Pack begin their championship run in Philly as they face "Comeback Player of the Year" Michael Vick and the Eagles' explosive offense.
rfid hacking protection|how to stop rfid scanning